You probably heard someone tell you to change your password. Well, in this article, I will try to demystify the world of passwords. This should give you a better appreciation about changing password length to subdue potential breach of your accounts by hackers.
A bit of history: Origin of passwords.
In ancient times, when villages were fending off invaders from every which way, villagers used to trade password, or “watchwords” to allow them into a camp or fortified villages. Failure to provide a valid password would most likely label you as a spy and cost you your life.
The Roman military innovate password technology by implementing password request (Which was a challenge) to obtain another password (Challenge response), which verified the chain of trust. They also kept tablets who they used to mark the password exchanges and keep track of duties. The Romans also used and developed encryption technology, but that topic will be for another article.
Computers
 The use of a password on a computer first appeared in the early 60’s. Access control was then developed requiring a USERNAME and a PASSWORD to validate access and give proper privileges to the system. Asking someone to choose a secure password in the ’60 was no different than is it today, except that the very thing passwords were supposed to be protecting (computers), started to be used to perform dictionary attacks to guess passwords and provide unauthorized access.
The use of a password on a computer first appeared in the early 60’s. Access control was then developed requiring a USERNAME and a PASSWORD to validate access and give proper privileges to the system. Asking someone to choose a secure password in the ’60 was no different than is it today, except that the very thing passwords were supposed to be protecting (computers), started to be used to perform dictionary attacks to guess passwords and provide unauthorized access.
What’s a dictionary attack exactly? Here’s an example. If I think of a word and ask you to guess that word, it would probably take you days, weeks, months of attempts before you finally guess it. However, computer can go thru a file containing dictionary words and process vast amounts of guesses with a good probability of success within a short time.
Obviously, a computer dictionary attack against a human would work because of our limited ability to process the attacking computer’s attempts. But if MY computer was holding the secret word and being attacked, it would be able to confirm or deny the attackers “password” in record times!
What if my computer password wasn’t a word from the dictionary, but a combination of letters, numbers and special characters, would that make the attack less successful? Yes. Hackers will use the easiest and quickest attack methods first, and then move to a more complex methods alternatively. A dictionary attack is easy because it’s fast and most of us still use words from a dictionary for passwords.
In case of failure, a hacker would then process to a brute force attack, trying to guess your password by trying every possible combinations progressively. This method is slower than a dictionary attack, but can provide fast results if the password length is small.
For example, the Oxford English Dictionary holds a bit less than 500,000 entries. The English language, approximatively 1 million words. If a hacker would use such lists, it would take him no more than 1 million attempts to guess the password. At computer speeds, that task can be performed in relatively no time.
Alternatively, If we create passwords using random letters, number and special characters, attacker’s computers can be programmed to go thru combination of letters, number and special characters in any form of incrementing size and every possible permutations.
Let’s say our secret password is “Z9p$2P78”. An 8 character password a human can remember.
The attacking computer doesn’t know the length of our password, so it should attempt every possible permutations, assuming your password length has only 1 character, then will try again using 2 characters, then 3, then 4…and so on, until it finds a match.
The attacking computer will try A, B, C, …. A1, A2, A3…. A!, A@, A#, …. AB1, AB2, AB3… and so on until every possibilities are covered. This is called a brute force attack. How many possibilities are we talking about in this example?
Assuming we are using all characters found in an extended ASCII table, the possibilities are 255 x 255 x 255 x 255 x 255 x 255 x 255 x 255, or 255^8 (255 to the power of 8), which equals: 1.7878103e+19, which equals 17 878 103 000 000 000 000 possibilities. At one point in time, that was considered a very large number. For you and me, going thru all possibilities would be impossible in many lifetimes. But for a computer, especially the modern systems available today, which can process billions and trillions of calculations per seconds, these powerful systems would make short work of our 8 characters password.
But some of you might say, wouldn’t a system administrator notice millions and billions of logon attempts on its systems? Yes, of course. Many years ago, I remember catching in the act hackers attempting dictionary attacks on a computer facing the internet. One of the easy countermeasure was to limit the number of login attempts per minutes before blacklisting the attackers IP.
This brings us to the reality of how can a hacker perform attacks without being observed?That’s where the concept of HASH comes in and is one of fundamental function used in computer security today.
HASH Function
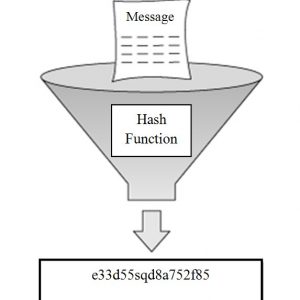 A hash is an encoding function of data, with a fixed size, used in hashing any types of data (Files, images, sounds..etc). When a piece of data is hashed, the output is a fixed number representing that uniqueness of that file.Think of it as the genetic code of your data. A finger print of sort. A hash is often used to validate that something has not been tampered with, that nothing within itself has changed, and does this by calculating and providing a hash function. If a hash is calculated on the original data, its has number will never change over time If it does, then you know something has changed within that data. Clever, right?
A hash is an encoding function of data, with a fixed size, used in hashing any types of data (Files, images, sounds..etc). When a piece of data is hashed, the output is a fixed number representing that uniqueness of that file.Think of it as the genetic code of your data. A finger print of sort. A hash is often used to validate that something has not been tampered with, that nothing within itself has changed, and does this by calculating and providing a hash function. If a hash is calculated on the original data, its has number will never change over time If it does, then you know something has changed within that data. Clever, right?
I’m sure you have downloaded a software from the internet and noticed the manufacturer providing a Hash number. Well this allows you to validate the data you have downloaded by creating your own hash function on the received data, and assure that it not been altered during the download process. Now you know what a hash function is used for.
There are many hash functions, and each have particularities: 1) One a hash has been created, it cannot be used to reverse calculate the original data. 2) There is only 1 possible hash result for every possible data input.
As an example, if I use an MD5 hash function (32 HEX Chars) to generate a hash of the letter “A”, the output will look like this:
Input: “A”
Hash Output: 7FC56270E7A70FA81A5935B72EACBE29
Input: “Ab”
Hash Output: 0E4C46DF226B9C0CB391311C54F28EFE
Notice how completely different the hash function is when I added only 1 letter. Now let’s try this with a whole file, a colour JPEG image of the Canadian flag;
Input: canada-flag.jpeg image file
Hask Output: 3CBBCC813004B3C4BF54C18E1BC01C5F
Input: canada-flag.jpeg image file, but after I change the colour of 1 pixel.
Hash Output: B422AD32F41FA0B7E70EF9AB486D443D
You will noticed that in the case of hashing a jpeg file, a very small change generates a whole new hash. Since there can be only 1 hash result for every possible data input, getting the same hash using 2 different source of data is called a HIT. Too many hits and upgrading the hash function is recommended.
Also, advancement in mathematics and computing power will render a hash function insecure over time. It is IMPORTANT to know that in our example, MD5 is no longer used and has been replace by SHA2 functions. A SHA256-SHA512 is currently the desired hash function used on the internet. But for our purpose, we will be using a simple hash function, MD5.
Any respectable websites will NEVER store the passwords of its users in cleartext. In our case, the password example used above, “Secret”, will be processed and the calculated hash will be stored on the website databases.
Username: cyberinsight
Password: Secret
Stored MD5 hash: 1E6947AC7FB3A9529A9726EB692C8CC5
With this in mind, when the user “cyberinsight” wants to login the website, a bank for example, the user types his password “Secret” and this password’s MD5 Hash is computed as “1E6947AC7FB3A9529A9726EB692C8CC5”, which is then compared with the value stored within its database. If the numbers are matching, then the password is assumed to be valid and the user is allowed in.
But remember, a hash is (was) technically impossible (or very very hard) to reverse. This is no longer true for some of the older hash functions. For example, if we hash the word “Secret”, and get the result hash “1E6947AC7FB3A9529A9726EB692C8CC5”, a hacker can easily put the value “1E6947AC7FB3A9529A9726EB692C8CC5” into an MD5 has function dictionary attack software and find out that your password is the word “password”. This is because someone bothered with creating an MD5 hash of the whole bloddy dictionary!
Take note that MD5 is now considered a very weak Hash function since the function algorytm has been broken.
If a hacker gets a hold of your password hash, he can perform one of several types of attacks to discover your real password. A dictionary attach is one method and can produce results in seconds. Another is a brute force attack, which consist of try every possible permutation of characters until there is a match. This can take longer to do for a computer, depending on how many characters your password has in its length.
Here is a list showing how long it can take a hacker to break your password using a brute force attack on the hash they stole;
Password with 7 characters or less, < 1 second.
Password with 8 characters, +- 5 hours
Password with 9 characters, +- 5 days
Password with 10 characters, +- 4 months
Password with 11 characters, +- 10 years
Password with 12 characters, > 200 years
… and each time you add a character to your password’s length, the time it takes to break it grows exponentially…
A password which took 3 years to break using brute force attacks in the year 2000, only take minutes in 2022. This is because computing power have greatly increased over 20 years. This demonstrates how weak our password protection have become if we don’t keep up with the advancement of technology.
The CSE (Canada) and the NSA (USA) use computers thousands of time more powerful in attempts to break into hash functions and adversary’s encrypted data. Therefor, the 200 years cracking time required for a 12 characters password may take minutes/hours for one of these super computers to process. As an advisory warning, longer and more complex passwords will eventually become obsolete and we will require better and more sophisticated methods, which will be discussed in part II of this article.
Password length
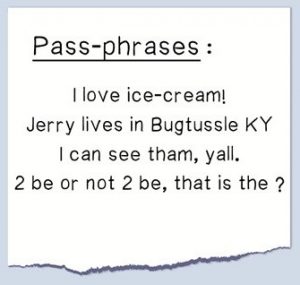
I hope you realize by now how password length affect the amount of work required to break into your valuable data! You might ask yourself “But how can I remember longer combination of characters”? Well, consider the following: A PassPhrase will make your passwords much longer, and easier to remember.
 For example, if we increate our above password example of 8 characters, “Secret”, and increase it to 12 characters, “SecretPW$x”, it will make it more resilient to brute force attracts, but makes it a bit harder to memorize.
For example, if we increate our above password example of 8 characters, “Secret”, and increase it to 12 characters, “SecretPW$x”, it will make it more resilient to brute force attracts, but makes it a bit harder to memorize.
PassPhrase
Now, take the following phrase: “Blue Man Group Make Music”. This password, or PassPhrase”, contains 25 characters (Including spaces) and would take quadrillions of years to brute force attack, and is easy for humans to remember.
This should convince you to change your passwords to at least 16 characters (Minimum length recommended), and specially use PassPhrases to facilitate memorizing. Four words of 4-5 characters would be best. The longer the passphrase, the better. Any respectable hackers will tell you that passwords cracking techniques make it possible to crack any password length today. Maybe, maybe not, but they will have a hard time cracking a 30 character PassPhrase.
There are additional methods you can adopt to protect against growing numbers of attacks. Remember that financial rewards and low risks is what motivates modern hackers and they want to get to your money and they have the tools to do it. Why make it easier for them?
If your password is your favourite pet’s name and is 5 characters long, please rethink your strategy! Let say your cat’s name is “Meow”, which happens to be your favourite password too, you can easily change that password to a PassPhrase! Something like: “Meow often makes noise at 3am!“, and at the same time, make it very hard to break using brute force attacks, and still make it easy for you to remember.
In the next article (Password Change – Part II), I’ll discuss the options you can adopt to effectively combat all kinds of password attacks and increase your security.
Brute force attack test
If you would like to test your password’s vulnerability, you can visit the following website: https://www.security.org/how-secure-is-my-password
Warning! Do NOT use your REAL passwords on that site. Just type a similarly built fake password (In length and characters types). That website will tell you how long it would take to brute force attack your password. Most people will decide to change their password management policy after visiting that site.
Factors of authentication
 The term “Factor” is defined as a circumstance, or a condition. In our case, a single factor authentication process means that a system will use only 1 (one) condition to authenticate you and allow access. Two-factor authentication means that a system will need 2 (two) distinct conditions to authenticate you. As you may have figured out, the more factors there are, the better the access security will become.
The term “Factor” is defined as a circumstance, or a condition. In our case, a single factor authentication process means that a system will use only 1 (one) condition to authenticate you and allow access. Two-factor authentication means that a system will need 2 (two) distinct conditions to authenticate you. As you may have figured out, the more factors there are, the better the access security will become.
In the security industry, it is often said that the best security is to challenge you to something you know, something you have, and something you are. These compounded factors assure that in any event that one of your factor is compromised, the remaining ones will still protect access to your account.
Something you know
Obviously, we are referring to passwords, or pass phrases, which is the first line of challenge to authenticate you and to allow you access. Unfortunately, many systems still use a single factor method to allow its user access to critical data. But this is slowly changing as the hacking industry is growing exponentially and influencing security professionals to react and improve their security controls. Society’s consensus will make multi-factor authentication obligatory eventually and companies who don’t commit to these new laws will not be insurable, become liable and fineable. This will become true for all internet facing networks. What happens inside you own private network is another matter.
Something you have
 By this, we are referring to something you carry with you, or can also be a secondary password verification using a temporary token. For many years, organizations wanting to protect their network assets, provided its users with a number generator to enforce a secondary authentication factor. These token generator often looked like an electronic fob, which was synchronized with the server side central fob, and upon pressing a button, would generate a random number which would then be entered as a secondary password. These numbers are generated by algorithms, which only the server side central fob and the user’s fob should know. These random numbers would be valid for a short period of time (Ex: 60 seconds), and failure to input that number in time would force you to press the fob’s button again and get a new one.
By this, we are referring to something you carry with you, or can also be a secondary password verification using a temporary token. For many years, organizations wanting to protect their network assets, provided its users with a number generator to enforce a secondary authentication factor. These token generator often looked like an electronic fob, which was synchronized with the server side central fob, and upon pressing a button, would generate a random number which would then be entered as a secondary password. These numbers are generated by algorithms, which only the server side central fob and the user’s fob should know. These random numbers would be valid for a short period of time (Ex: 60 seconds), and failure to input that number in time would force you to press the fob’s button again and get a new one.
The problem with these physical fobs is the cost. Many years ago, these fobs would cost hundreds of dollars, and the company you worked for would have to provide one to every employees, increasing the cost of security tremendously. You can get a token fob system implemented for approximatively $50 per unit today.
But an elegant alternative exist today in the form of communicating random numbers via a mode of communication most of us owns, a cellular phone. In the process of two-factor authentication, the server can generate a random number and send you that number thru another mode of communication, either Text SMS, or email, or even call you on your telephone and announce the number vocally. This method is slowly becoming the preferred method of two-factor authentication simply because of availability and low cost.
You can’t decide to start using multi-Factor authentication unless it is provided by the service you are connecting to. My banks for example, have been slowly introducing a two-factor authentication service, first, with adding secondary questions, like “What is your pet’s name”, and eventually, a full two-factor authentication using token numbers sent via SMS or Email.
In the case of a corporate VPN connection for example, a user certificate could be automatically issued, uploaded to that user’s laptop, and managed by the company’s Active Directory group policies. This method would allow a user to connect to the corporate network remotely using a password only, while maintaining the factor of authentication’s integrity by automatically leveraging that user certificate as a secondary authentication token by the VPN connection software. I’ve implemented this type of VPN authentication at my last job and it works very well. Each issued certificates were also used to perform identity based policies.
Something you are
 To increase the effectiveness of the authentication process, a 3 (three) factor authentication method, or something you are, can be introduced. By something you are, I mean a characteristic of your own person; eyes, face features and/or finger prints. This is also referred to as Biometrics.
To increase the effectiveness of the authentication process, a 3 (three) factor authentication method, or something you are, can be introduced. By something you are, I mean a characteristic of your own person; eyes, face features and/or finger prints. This is also referred to as Biometrics.
This method is not readily deployed because of the complexity to develop and implement, but rest assured, modern smart phones being used by almost everyone on this planet, will make this authentication method more accessible and there will be a day where your smart phone will ask you to look into screen (camera) to validate your face features, or even be able to perform retinal scans or finger print readings. Many smart phones today already offer these features to authenticate the owner of the phone.
Are the 3-factor authentication method described enough to provide the factor security scenario? Of course not, but they are pretty good, good enough to discourage any criminal entities to venture into attempts to to circumvent a 3-factor authentication system.
But if you are old enough to remember the old TV show “Mission Impossible”, you will realized that the goal justifies the means, and there will always be some well funded criminals willing to try to outsmart the system. In this case, we just hope that the cybersecurity good guys will outsmart the bad ones.
Salting passwords databases
Salting a database is a term that defines “adding something to the mix”. Any company that respects you will put additional security to protect your stored password in its database by taking your password HASH, add 32 characters to it, and HASH it again it before storing the final HASH in its database. That practice helps against being able to reverse calculate weak passwords in the case the database is compromised and/or stolen by threat actors. By this practice, even a weak password such as “hello123” is renders impossible to reverse calculate.
Peppering passwords
It involves adding random data or characters to the plaintext password before it is hashed and stored in a database. The added data is not included in the authentication process, but it makes it more difficult for attackers to guess or crack the password using brute-force or dictionary attacks.
Unlike salting, which uses a unique value for each password, peppering uses a single global secret value that is shared across all passwords. This approach requires additional precautions to keep the secret value confidential and secure, as its compromise would put all passwords at risk.
Peppering is not a widely used technique in modern password storage systems, as it is considered less secure than salting, which provides better protection against attacks such as precomputation and targeted attacks.
Manage your Passwords
In conclusion, if changing your password to a PassPhrase or adopting a multi-factor authentication system isn’t your thing, may I recommend you at least the use a Password management tool. I’ve adopted one for the past few years now and it made my life much easier.
Like many of you, I used to have a traditional method of managing my passwords, but the more I researches cybersecurity, the less attractive that method appeared to be. I then decided to use a password management software called “KeePassCX” to help me sort out my and manage my passwords and finally put a level of trust in this tool.
 KeyPassXC is a small and very secure tool, it allows you to centralize and manage ALL of your passwords. Its has smart features and encrypts your valuable passwords like a pro. Since I started using this tool, I only have to remember one very important password, the password (Or PassPhrase) allowing me to open the KeePassXC database. For this, I use a long PassPhrase, a phrase I will never forget and which is long enough to survive any dictionary or brute force attacks.
KeyPassXC is a small and very secure tool, it allows you to centralize and manage ALL of your passwords. Its has smart features and encrypts your valuable passwords like a pro. Since I started using this tool, I only have to remember one very important password, the password (Or PassPhrase) allowing me to open the KeePassXC database. For this, I use a long PassPhrase, a phrase I will never forget and which is long enough to survive any dictionary or brute force attacks.
The moment I started using this tool, I went thru ALL my known accounts (Local and online), one by one, wrote detailed information about each accounts and proceeded with changing passwords of all those accounts. This time, KeePassXC randomly created the passwords for me and I made them extra long and extra complex.
Now, upon connecting into an online service, I open KeyPassXC and copy & paste my credentials and password with a click of the mouse. KeePassXC is smart, as it clears automatically any traces of your copied password from your computer, except the one store in its database of course.
As an example, I might have a Facebook account and changed my login account password to “dim+e)\B?r}]HVyDjuaGP+G3!}>OuO;GkirQ_8q9“. I don’t have to remember this long string, my computer does all the work! KeepassXC does PassPhrase too! With a simple clic, KeePassXC can generate a new complex PassPhrase for that Facebook account, which now looks like this: “lingo unfrosted anointer zealous reprint stoneware glory dingy“. But what’s the point of using PassPhrases if you are going to generate 50 characters long passwords? Random character passwords are better than password composed of dictionary simply because dictionary attacks are usually attempted first.
If you use centralized password management like KeyPassCX, make frequent backups of the database, copy it on a USB Fob and place this Fob somewhere it cannot be destroyed by an accident, like a fire for example. Since the database is well encrypted, you can also upload a copy of your KeepassXC database to your OneDrive or iCloud account. It will be safe there.
There are many password management tools available for all platforms. I would recommend NOT using an online password management service. They’ll promise convenience for a small fee, but you’ll be the goose if/when their servers gets breached.
In conclusion, I recommend watching the following YouTube clip, a clip produced by Ricky Tan of Cyberspatial, and is no doubt in my mind the best clip about password management tools.
This was my view.
CC

